Written by Youngjin Hwang on 05/11/2021
Nowadays, browsing the internet with PCs or our smartphones has become an essential part of our daily life. As a result, it is possible to peek into the data being transmitted over the Internet with malicious intent. In other words, being able to peek at the data being transmitted by someone is called sniffing.
A classic example of a sniffing attack would be intercepting the account’s id and password and causing physical damage by using the personal information of others.
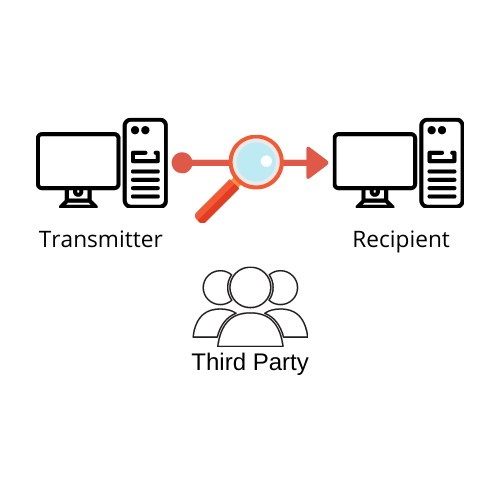
To protect our database user data, CUBRID 11.0 has enhanced security by providing packet encryption (and TDE (Transparent Data Encryption) based data encryption, but that will be cover in another blog later). When packet encryption is applied, the packet is encrypted and transmitted for the data to be transmitted, making the data uninterpretable even if someone sniffs it.
CUBRID PACKET ENCRYPTION
CUBRID uses SSL/TLS protocol to encrypt data transmitted between the client and server. SSL encrypts data sent and received using a symmetric key, in another word, the client and server share the same session key to decrypt.
Whenever a client connects to the server, an asymmetric encryption algorithm is used to exchange information required to generate a newly created session key in an encrypted form. For this purpose, the server's public key and private key are required.
The public key used by the server is included in the certificate ‘cas_ssl_cert.crt’, and the private key is included in ‘cas_ssl_cert.key’. The certificate and private key are located in the $CUBRID/conf directory. This certificate was created using OpenSSL's command tool and is a ‘self-signed’ certificate.
This certificate, ‘self-signed’ certificate, was created with the OpenSSL command tool utility and can be replaced with another certificate issued by a public CA (Certificate Authorities, for example, IdenTrust or DigiCert) if desired. Or existing certificate/private key can be replaced by generating a new one using the OpenSSL command utility.
Below is an example of creating a private key and certificate using the OpenSSL command tool.
|
# create 2048 bit size RSA private key
$ openssl genrsa -out my_cert.key 2048
# create CSR (Certificate Signing Request)
$ openssl req -new -key my_cert.key -out my_cert.csr
# create a certificate valid for 1 year.
$ openssl x509 -req -days 365 -in my_cert.csr -signkey my_cert.key -out my_cert.crt
|
cs |
And replace my_cert.key and my_cert.crt with $CUBRID/conf/cas_ssl_cert.key and $CUBRID/conf/cas_ssl_cert.crt respectively.
(The self-signed certificate example written above is a certificate that is valid for one year and must be renewed every year. If you do not want to renew every year, since the self-signed certificate does not need to be renewed every year if you increase the validity period, you can change the validity period of the self-signed certificate. You can increase it or use it instead of a certificate issued by an accredited certification authority.)
CUBRID PACKET ENCRYPTION METHOD
- Supported drivers:
CUBRID provides various drivers, but the drivers that support packet encryption connections are JDBC and CCI drivers.
- Server setting:
CUBRID can set the encryption mode and non-encryption mode on a per broker basis. The default is the non-encryption mode, and you can set the encryption mode by changing the SSL parameter value of cubrid_broker.conf in the configuration file to ON as shown in the figure below.

The client (AP application) can make an encrypted connection using the useSSL property of db-url. Clients can connect to SSL by simply adding the useSSL property as shown in the example below.
|
JDBC driver : "jdbc:cubrid:localhost:33000:demodb:::?charset=utf-8&useSSL=true","UserId",""
CCI driver : cci:cubrid:localhost:33000:demodb:::?useSSL=true
|
cs |
- CUBRID Manager:
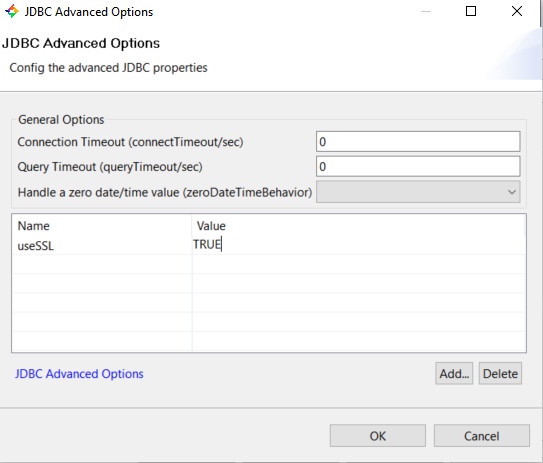
If the broker is used without setting the useSSL property while operating in encryption mode, the following error will be displayed. This means that the client you are trying to connect to and the broker encryption mode must match (both in encrypted mode or both in non-encrypted mode).
The requested SSL mode is not permitted, the CAS server is running in a different mode (check useSSL property).
BEFORE/AFTER APPLYING PACKET ENCRYPTION
- Before:
The picture below is when packet encryption connection is not applied. If you look at the TCP stream, you can see the query and results used.

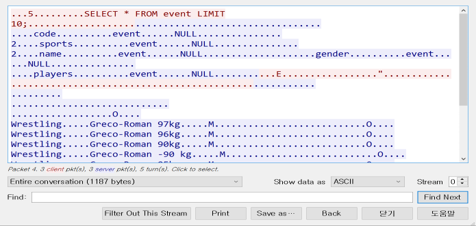
- After:
The picture below is a screenshot after applying the packet encryption connection. In this case, displayed query and result values are encrypted and cannot be interpreted.



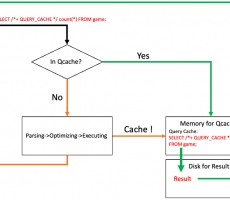
 QUERY CACHE Hint
QUERY CACHE Hint
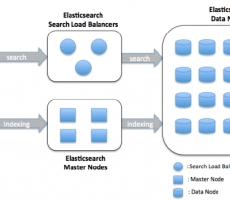
 Our Experience of Creating Large Scale Log Search System Usin...
Our Experience of Creating Large Scale Log Search System Usin...